Reserve heist takes BB back to manual foreign payment
Fed warns of cutting off transactions if the Bangladesh Bank fails to rebuild SWIFT network by June next year

Highlights:
- Bangladesh Bank operating foreign transactions manually after cyber hacking
- Fed warned of cutting transactions with the Bangladesh Bank
- SWIFT network will have to be rebuilt by June next year to continue transactions with Fed
- Fed already curtailed transaction days of Bangladesh Bank
- SWIFT officials have not visited the Bangladesh Bank since the cyber hacking
- Rebuilding SWIFT messaging network requires physical presence of SWIFT officials
The Bangladesh Bank has not been able to rebuild its compromised foreign transaction messaging network, otherwise known as SWIFT, even five years after it lost $81 million to cyber hacks, according to various documents and interviews available to The Business Standard.
The central bank has been left with no option but to conduct foreign transactions manually – something without an instance in the world.
The Federal Reserve Bank of New York has now warned that it will cut off transactions with the Bangladesh Bank if the SWIFT network is not re-built by June next year.
The central bank's transaction days are already curtailed. As a result, on several days a month, it has to conduct transactions with the help of a locally-based foreign bank paying a charge.
If the Fed shuts the transactions, the Bangladesh Bank will have to make all foreign payments through a third party, which will hurt its reputation.
The Bangladesh Bank has to make foreign transactions manually as SWIFT has not yet sent its officials to assist in rebuilding its network, causing disruptions for the central bank.
Short for Society for Worldwide Interbank Financial Telecommunication, SWIFT provides a vast messaging network used by banks and other financial institutions to quickly, accurately, and securely send and receive information, such as money transfer instructions.
SWIFT's messaging services are used by more than 11,000 financial institutions in more than 200 countries and territories around the world.
SWIFT is the only option for the Bangladesh Bank to execute foreign payments with the Fed.
When contacted, Bangladesh Bank Governor Fazle Kabir said, "Rebuilding of SWIFT infrastructure is on. A third party audit is needed, which is now being done."
"We are ready to rebuild the SWIFT system by purchasing all necessary devices, only SWIFT needs to send their officials for deployment," said Ahmed Jamal, deputy governor of the Bangladesh Bank.
SWIFT also wants to send their officials, but they want a guarantee that police will not harass them regarding the cyber heist case when they visit Bangladesh. But Bangladesh police do not want to guarantee that – causing a delay in rebuilding the SWIFT system, he noted.
The Bangladesh Bank is now making foreign transactions manually to avert risk that costs higher for receivers, he added.
The central bank cannot run the manual system for long as the Fed has already warned that they will shut the payment system if the SWIFT system is not rebuilt, Ahmed Jamal said.
What SWIFT says
The Business Standard sent an email to SWIFT seeking its opinion.
The mail read: The Bangladesh Bank did not rebuild SWIFT infrastructure after the cyber heist owing to not having physical assistance from SWIFT. The completion of the system's rebuilding requires physical presence of people from SWIFT, but no one has visited the Bangladesh Bank since the cyber heist. What is your opinion in this regard?
SWIFT replied: "As a neutral provider focused on supporting the entire global financial community, SWIFT continues to work with the Bangladesh Bank and stands ready to support the central bank in transacting across borders safely and securely."
TBS contacted Andrea Priest, VP and head of External Communication at the Federal Reserve Bank, requesting comments over the manual transaction system of the Bangladesh Bank.
In reply, she said, "We do not comment on account holders."
How Bangladesh Bank is executing foreign transactions now
Under the manual process, the Bangladesh Bank has to maintain three steps for a foreign payment through the SWIFT network.
In the first step, a SWIFT message is generated for making a payment and in the second step, the designated central bank officials confirm the message through an email to the receiver. In the third step, a Bangladesh Bank officer makes a phone call from a specific number to the receiver to execute the payment.
If the SWIFT infrastructure is built, foreign payments will be executed only through automated messaging.
In the manual system, the receiver has to designate an officer for confirming the email and attend the phone call to execute the payment, which is costly for payment receivers as they have to deploy extra manpower only for transactions with the Bangladesh Bank.
After long years of manual operation, the Fed came up with the warning as it executes a large number of transaction orders from across the world daily through SWIFT automated messaging system, but it has to deploy an official only for the Bangladesh Bank to execute its transactions.
It is not cost effective to deploy extra manpower for the Fed as the Bangladesh Bank's transaction volume is not significant for the receiver, said a senior executive of the central bank.
The Bangladesh Bank has to execute 50 to 200 foreign transactions daily, including government ones.
The Fed has already reduced transaction days for the Bangladesh Bank owing to its manual system.
The Bangladesh Bank cannot execute transactions with the Fed on all transaction days. One or two days a week, it has to make payments through a foreign bank operating in Bangladesh, which is harming the reputation of the central bank. On top of that, the Bangladesh Bank has to pay commission to the foreign bank for executing the payment.
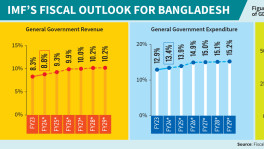
Raising concern about the IT security risk, the International Monetary Fund (IMF) in its draft report on safeguards assessment of the Bangladesh Bank for 2021, said despite unrecovered losses from the 2016 cyber heist, the Bangladesh Bank has not finalised the rebuilding of SWIFT infrastructure and the integrity of its IT environment remains disputable.
Why delay in rebuilding SWIFT infrastructure
Soon after the reserve heist, SWIFT introduced a customer security programme for all its customers worldwide under which all users will have to conduct a yearly audit of IT security of the SWIFT system.
Even though SWIFT's development came after the Bangladesh Bank's reserve heist, it did not take any responsibility for the heist or did not clarify if the theft was for any security loophole of the SWIFT service.
On the other hand, SWIFT and the Fed jointly recommended that the Bangladesh Bank rebuild the SWIFT infrastructure to remove malware in the system. This recommendation was only for the Bangladesh Bank.
After rebuilding the system, the Bangladesh Bank will have to audit the whole system by any of seven global auditors, including Deloitte, PWC, or KPMG, according to the recommendation.
After the final audit, the Fed will allow the Bangladesh Bank to use the SWIFT network for transactions.
The Bangladesh Bank has already purchased necessary devices to rebuild the system following the recommendation of SWIFT. The deployment of the products requires physical presence of SWIFT personnel to assist in rebuilding the system. But SWIFT has not sent their officials to Bangladesh since the cyber heist. As a result, the central bank could not rebuild the system, according to central bank officials involved with the process.
Meanwhile, the central bank partially set up the system taking assistance from SWIFT over phone, but it needs an authorisation of whether the system is now out of risk.
To get the authorisation, the Bangladesh Bank appointed an auditor named Enterprise InfoSec Consultants (EIC) in May this year following the recommendation of SWIFT to audit the IT security of the SWIFT system. The EIC, a listed audit firm of SWIFT, started operation in Bangladesh in 2016 and dealt with the Bangladesh Bank to submit the report by 78 days or in two and a half months. However, the audit firm did not submit the audit report even in six months.
This reporter visited the office of the company to talk over the audit issue, but the owner of the company refused to meet or talk to her over phone.
How vulnerable is the overall IT environment of the Bangladesh Bank
When the Bangladesh Bank could not ensure the security of foreign payments even after cyber hacking, questions arose about security of the overall IT environment of the central bank.
The IMF in its safeguards assessment report mentioned that the Bangladesh Bank should intensify efforts to identify and address cybersecurity vulnerabilities.
The Bangladesh Bank established its Cyber Security Unit (CSU) in 2020, four years after becoming the victim of the biggest cybercrime.
The delay in establishing the cybersecurity unit was because no one with expertise in the IT sector was interested in working with the central bank after the cyber heist, said a senior executive of the Bangladesh Bank.
The central bank issued a circular three times to hire an IT expert for the CSU but did not find any suitable candidate, he added.
Central bank high officials requested many well-reputed IT specialists to join the Bangladesh Bank but they denied, he also said.
Finally, the central bank appointed a certified IT system auditor as the head of the CSU.
The CSU has started developing the ICT risk management framework and performing vulnerability assessments penetration tests of the Bangladesh Bank system, according to officials.
While the Bangladesh Bank has been suffering from legal tangles after the reserve heist, there is no progress in recovering the stolen money or in the cases filed with both local and international courts.
The Criminal Investigation Department (CID) did not submit the charge sheet following its investigation even six years after a case was filed by the Bangladesh Bank on 15 March 2016.
On 31 January 2019, the Bangladesh Bank filed a case against the Rizal Commercial Bank with a US court for the Southern District of New York, but there is not much progress on it, said a senior executive of the Bangladesh Financial Intelligence Unit, the department involved in dealing with the international case.
On 4 February 2016, hackers stole $101 million from the Bangladesh Bank's accounts with the Federal Reserve Bank of New York.
Of the amount, $81 million was transferred to four accounts with the Rizal Commercial Banking Corporation (RCBC) in Manila and another $20 million to a bank in Sri Lanka.
However, the transfer of $20 million to Sri Lanka failed because of a spelling error by the hackers. The Bangladesh Bank got back that amount from Sri Lanka.
Later, the Bangladeshi central bank was able to retrieve about $15 million from the amount the Philippines realised in fine from the RCBC for its negligence in duty. About $66 million could not be recovered yet.


 Keep updated, follow The Business Standard's Google news channel
Keep updated, follow The Business Standard's Google news channel